Telegram has modified the login process on a new device: from now on, it is only possible to receive code via connection if the user has 2-step verification enabled. The move had been confirmed in the official messenger account on Twitter, last Friday, the day after the arrest of four people accused of involvement in the case of a breach of official cell phones, including Minister Srgio Moro.
According to the Federal Police, hackers would have used the technique called spoofing to trick operators into accessing the mailbox of attacked lines and listening to the authentication numbers provided by the app via phone call. With the change in procedure, valid in the versions of the Android and iPhone (iOS) application, you can only get the code in this way by entering an additional password.
Operators correct breach that allowed authorities mailbox access

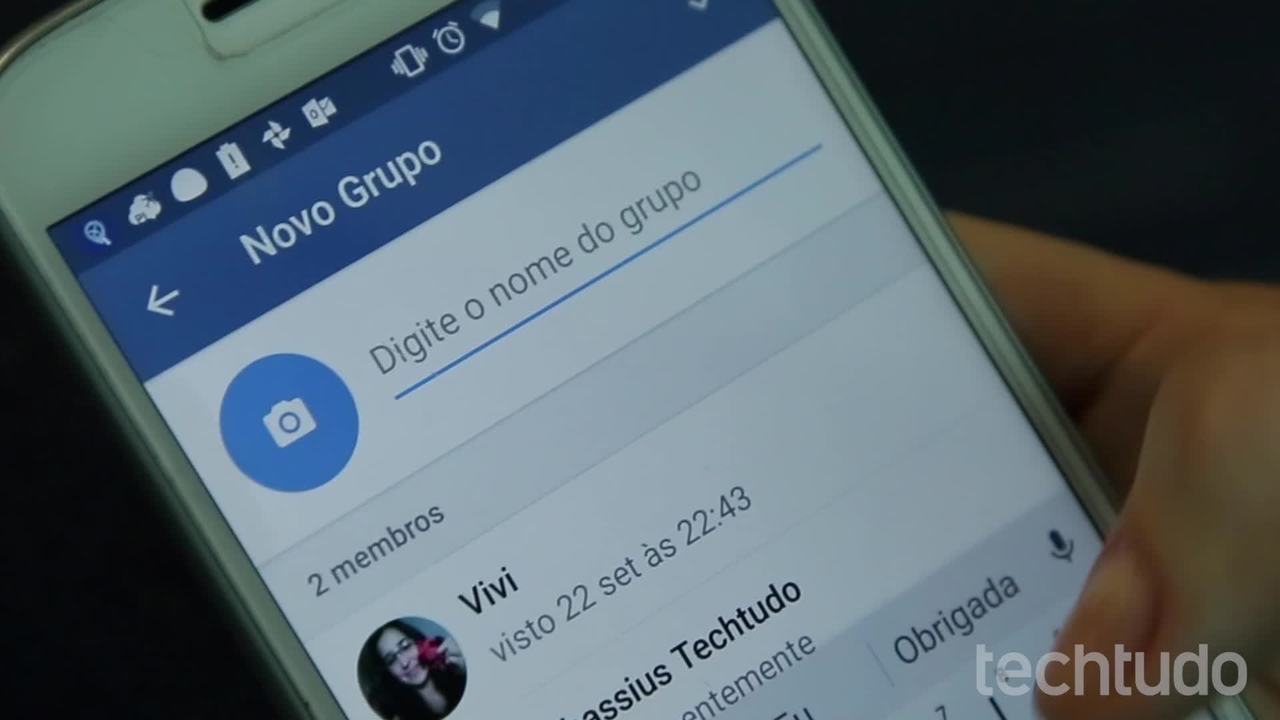
Telegram now sends code via call only to those who have verification in two steps Photo: Reproduction / Marvin Costa
Want to buy a cell phone, TV and other discounted products? Meet the Compare dnetc
According to Telegram, enough is not to worry if phone operators take too long to fix vulnerabilities in their voice mail system.
Upon entering the messenger on a new device, the app only offers to send code by call if the user enters the two-step verification password in sequence. If the account does not have protection set up, you can request numbering only via SMS or through another device that already has access to the profile.
Right. And don't worry if phone operators take too long to fix vulnerabilities in their voice mail system now, we only allow you to receive codes per call if you have enabled 2-step scanning.
– July 26, 2019
According to PF, hackers reportedly launched a feature called Caller ID Spoofing. The function spoofs the caller ID to make a call from a particular line appear with another number on the recipient's cell phone.
In breach of Moro's profile in Telegram, the accused would have used the technique to simulate a call from the minister himself to his mailbox and thus listen to the application verification code when a phone is unavailable (switched off or out of service), The app leaves a recording containing the numbering. The vulnerability in the operator's system would be precisely in not identifying the scam and freeing the attacker's access to the voice message.
It is suspected that the alleged victims of hackers would not have configured 2-step verification in the application. Enabling the feature would prevent account access even if the attacker had Telegram code via the link. With dual verification enabled, in addition to the code sent at login, I need to enter a password that, in theory, only the user knows.
Telegram: Four Curious Functions
