Phishing, cryptojacking and ransomware are examples of threats to which Internet users are subject. These criminal tactics are commonplace and responsible for much of the data theft online. However, seemingly harmless actions, such as connecting to a public Wi-Fi network or installing apps not available at official stores, can also pave the way for hacker attacks. Check out the list below for five digital security threats and how to protect yourself from each one.
READ: Major failure hits PCs 20 years ago; see if you take risks
What ransomware: five tips to protect yourself
Want to buy a cell phone, TV and other discounted products? Meet the Compare dnetc
Due to their easy application and ability to reach multiple users at the same time, phishing attacks are responsible for 90% of online thefts. In general, cybercriminals send fraudulent emails that appear to be from real bank companies, for example to mislead victims and trick them into opening malicious links or infected attachments. By biting the bait, the user has his personal data such as passwords, bank information and credit card number stolen by hackers.
Facebook fake emails can hide phishing scam to steal data Foto: Divulgao / Kaspersky Lab
While emails are very realistic and reproduce an interface very similar to authentic services, looking at some aspects can help determine if the message hides a scam. Firstly, it is important to check whether the source address actually corresponds to the sender: in many cases, emails carry typing errors (Amazod instead of Amazon, for example). Also, it is worth checking a site's HTTPS certificate before sending sensitive information and avoiding opening suspicious files.
Attracted by the ability to access online services away from home for free, many users connect to open Wi-Fi networks. However, this ordinary and seemingly harmless attitude hides a risk: criminals can create fake public networks to steal user data. From login, hackers can crawl all websites visited and even steal passwords and other personal information provided.
Criminals May Use Open Wi-Fi Networks to Intercept Personal Data Photo: dnetc
To avoid criminal interceptions, always use a virtual private network (VPN) to connect to the Internet. By encrypting the connection, VPN helps prevent third parties from accessing your device and capturing the data you send and receive. Never connect to Wi-Fi networks whose origin is unknown.
Download only apps available from official stores, such as Google Play Store Photo: Rodrigo Fernandes / dnetc
Fake versions of popular applications are often used by criminals to take money from users and steal personal data. In order to attract victims, fraudulent apps often promise unique functionality. The most effective way to protect yourself from these threats is to download apps only from official Google Play Store stores for Android phones and App Store for iPhones (iOS). Avoid downloading modified versions of apps that require unofficial APKs to work, such as GB WhatsApp: they can hide viruses or malware.
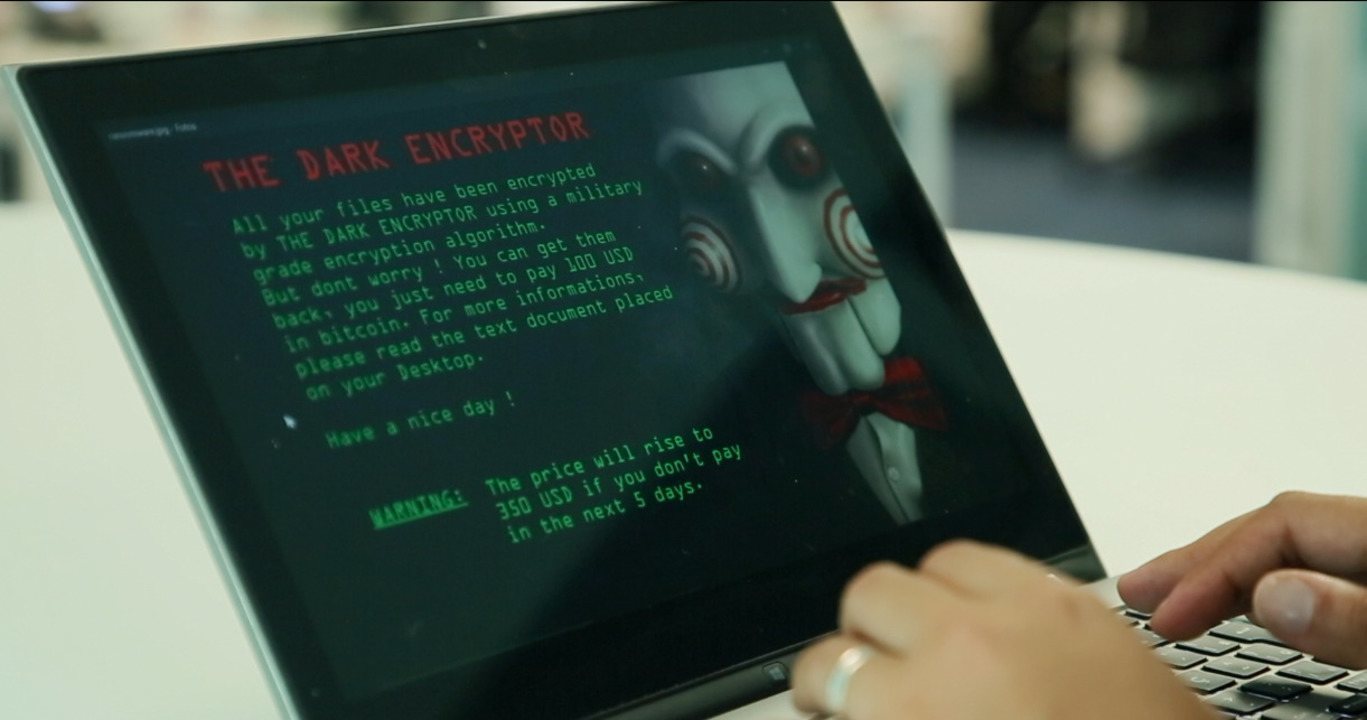
Ransomware is a particularly dangerous type of malware in which criminals encrypt victim files and charge cash for ransom, often using hard-to-track bitcoin virtual currency. The threat can be installed through malicious links to websites, emails and messaging applications. Sophisticated, this virtual hijacking mode can also involve blocking access to the user's entire operating system.
Computer infected with ransomware Photo: Joo Balbi / dnetc
There is a lot of care that can prevent ransomware infection. Verifying that the legitimate visited site is protected by HTTPS, not downloading files sent by unknown senders or hosted on suspicious pages, and keeping the antivirus always up to date are just a few.
The cryptojacking scam is to remotely exploit computers for virtual currency mining. The application of criminal tactics already exceeds the volume of ransomware attacks and brings significant damage to the user's machine. This is because the process of mining any cryptocurrency puts a heavy strain on the device hardware, causing slow and long-term component life. Cryptojacking also impacts energy consumption, which generates extra expenses on the electricity bill.
Cryptojackings are attacks aimed at using the user's device to generate virtual currencies for third parties. Photo: Divulgao / FISL
Some cryptojacking attacks require malware infections to function. To protect yourself, always keep your antivirus up to date and pay attention to the websites you visit and the files downloaded to your computer. Other scams, in turn, use web pages to mine Bitcoin. In this case, there are extensions for browsers that promise to block any attempt to hijack your system for mining.
How do I recover photos from APPLOCK app? Find out on the dnetc Forum.
